AWS SNS event configuration tutorial
This article steps you through configuring Amazon Web Services (AWS) for Pismo event notification delivery. This configuration requires you to create two things in AWS:
-
Simple Notification Service (SNS) topic: SNS is a managed service that provides message delivery from publishers to subscribers. Publishers communicate asynchronously with subscribers by sending messages to a topic, which is a logical access point and communication channel.
-
Identity and Access Management (IAM) role: An IAM role is an IAM identity that you can create in your account that has specific permissions. An IAM role is similar to an IAM user, in that it is an AWS identity with permission policies that determine what the identity can and cannot do in AWS. However, instead of being uniquely associated with one person, a role is intended to be assumable by anyone who needs it.
For this tutorial, you need:
- An AWS account
- Your Pismo Org ID (also known as tenant ID)
- AWS data account ID (from Pismo)
Configure AWS for Pismo event notifications
-
Log in to Amazon Web Services with your AWS account.
-
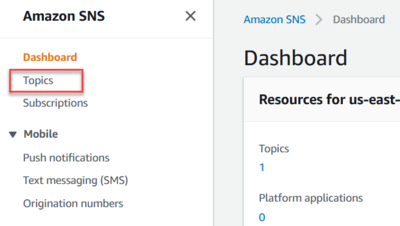
Go to the Amazon SNS dashboard (search for
SNS). -
In the sidebar, click Topics.
-
Create a new topic:
- Click Create topic.
- Make sure you click Standard as the type. This should come up as the default.
- Under Name, enter your topic's name.
- Click Create Topic.
- In the page that appears, note the ARN (Amazon Resource Name) field.
-
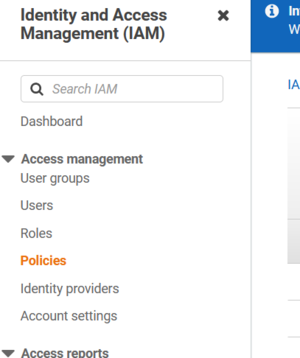
Go to the IAM dashboard. (Type IAM<enter> in Search and it appears.)
-
In the sidebar, under Access Management, click Policies.
-
Select Create policy in the upper-right.
-
Click the JSON tab and enter the following:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"sns:Publish"
],
"Resource": [
"arn:aws:sns:us-east-1:<your AWS account ID>:<newly-created topic name>"
]
}
]
}-
Click Next:Tags.
-
Click Next:Review and enter the policy name in the Name field.
-
Click Create policy.
-
Return to the IAM dashboard page.
-
In the sidebar, click Roles under Access Management.
-
Click Create role.
-
Select AWS account, then click Next.
-
On the page that displays, select the policy you just created and click Next.
-
On the Name, review and create page, enter a name for your role and then click Create role.
-
Contact your Pismo representative to provide the Amazon Resource Names for:
- IAM role. For example: arn:aws:iam::303421646629:role/test-pismo-integration-role
- SNS topic. For example: arn:aws:iam::<Your AWS account ID>:<your SNS topic>
Pismo will provide you with an IAM Role to complete the configuration.
Complete configuration with Pismo's IAM Role
You can complete this procedure after Pismo provides you with the necessary details, such as the Tenant/Org ID and external ID.
-
Return to the IAM dashboard home page and select Roles under Access Management. Then, click on the role you created for this integration.
-
Select Trust Relationships. In the text box that appears, click Edit trust policy and enter the following code:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::<AWS_DATA_ACCOUNT_ID>:role/dataplatform-lambda-fn-<TENANT/ORG_ ID>"
},
"Action": "sts:AssumeRole",
"Condition": {
"StringEquals": {
"sts:ExternalId": "<PISMO_PROVIDED_EXTERNAL_ID>"
}
}
}
]
}The Tenant/Org ID you enter here must be lowercase. The external ID is provided by Pismo.
- Click Update policy.
Updated about 1 month ago